Symptoms
Microsoft Outlook client crashes when opening Microsoft Teams meetings, or mousing over meetings without opening them.
Cause
This happens because Windows Defender Exploit protection prevents Outlook from growing beyond its assigned memory. This often occurs when Windows is running the Microsoft .Net framework 3.5 and other versions of .Net framework at the same time.
Workarounds
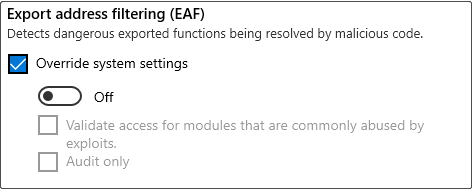
Turn off Export address filtering (EAF) or Import address filtering (IAF) in Windows Defender Exploit protection:
Method 1
Process for end-users:
-
Close all Outlook windows and any other Office applications.
-
In the Start menu, search, and open Windows Security.
-
Go to App & browser control.
-
Scroll down to the Exploit protection section and select Exploit protectionsettings.
-
Switch from System settings to Program settings.
-
Find outlook.exe in the list, select the entry to expand, and select Edit.
-
Scroll to Export address filtering (EAF) and turn it off.
-
Scroll to Import address filtering (IAF) and turn it off.
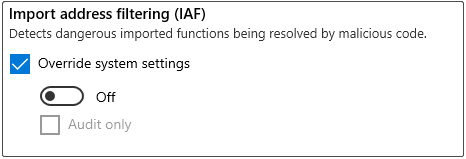
Check if the outlook client runs correctly. If it does, remove the check next to Import address filtering (IAF) to reset it back to the default system settings. Restart Outlook and see if it is still running correctly. By doing this, you can verify whether Export or Import is causing the problem.
Method 2
Process for administrators:
To disable this security mitigation, you can use a policy XML file. This is because both Intune and System Center Configuration Manager deployment depend on this file. The following policy XML settings must be updated to explicitly disable these mitigations. You can’t simply remove the payload line from the XML file. You must also set them to false as shown below:
<AppConfig Executable="outlook.exe">
<Payload EnableExportAddressFilterPlus="false" EnableExportAddressFilter="false"/>
</AppConfig>
For more information about how to deploy Exploit protection policies with System Center Configuration Manager, see Create and deploy an Exploit Guard policy.
For more information about how to deploy Exploit protection policies with Intune, see Protect devices using Intune.










