Symptoms
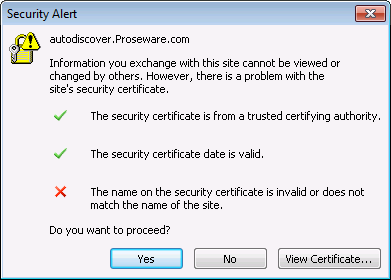
In a dedicated or International Traffic in Arms Regulations (ITAR) Microsoft Office 365 environment, a user is prompted by a Security Alert dialog box that includes the following error message:
The name on the security certificate is invalid or does not match the name of the site.
For example, the Security Alert dialog box resembles the following:
-
The user tries to create a new profile in Microsoft Office Outlook.
-
The user tries to start an Outlook client.
-
The issue occurs intermittently when the Outlook client is running.
If the user clicks Yes, the user can continue the operation. However, if the user clicks No, Autodiscover lookup fails. The failure of Autodiscover lookup prevents the following features from working as expected:
-
Automatic creation of an Outlook profile by using Autodiscover
-
Out of Office (OOF) Assistant
-
Free/Busy information
Cause
Generally, this issue occurs when the URL that you are trying to access is not listed in either the Subject or the Subject Alternative Name (SAN) of the Secure Sockets Layer (SSL) certificate for the website. Although different organizations' configurations may differ slightly, this issue typically occurs because the organization's Autodiscover Domain Name System (DNS) records are configured incorrectly.
Resolution
To resolve this issue, you may have to change your Autodiscover DNS records (internal, external, or both). However, these changes should not be taken lightly, because the Autodiscover feature may not function if DNS records are configured incorrectly. Before you change the Autodiscover DNS records, you should understand how the Outlook client tries to locate the Autodiscover service. The Outlook client tries to locate the Autodiscover service by using the following fundamental order of operations. However, the step in which the Autodiscover service is located varies from deployment to deployment. This location depends on whether there is an on-premises solution in co-existence and what the specific on-premises email environment is (for example, an on-premises Microsoft Exchange Server, an on-premises Lotus Notes, or another environment). The following table displays the fundamental order of operations for how the Outlook client locates the Autodiscover service:
|
1 |
|
|
2 |
|
|
3 |
|
|
4 |
|
|
5 |
Result If the Autodiscover service is not found by any of these methods, Autodiscover fails. |
In summary, the Autodiscover service may be resolved by using an A record, a CNAME record, or an SRV record. To determine which records are used currently, run the following commands at a command prompt or in Windows PowerShell:
-
To locate an A record, run the following commands. Make sure you substitute SMTPDomain.com below with the domain with the value at the top of your certificate error.
nslookup
set type=A
Autodiscover.SMTPDomain.com
-
To locate an SRV record, run the following commands:
nslookup
set type=SRV
_autodiscover._tcp.SMTPDomain.com
In the following example, the Outlook client can locate the Autodiscover service by using the A record for the Autodiscover URL as described in step 3 in the previous table:
autodiscover.proseware.com
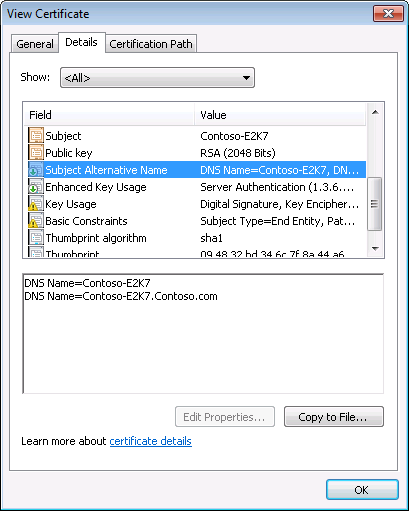
However, as we mentioned in the "Cause" section, this URL is not listed in the SAN of the SSL certificate that is used by the Autodiscover service. For example, see the following screen shot:
Replace the existing A record by using an SRV record that points to a namespace that is already in the SAN of the SSL certificate
This is the preferred resolution method in the current service design because the existing SSL certificate does not have to be updated and deployed. According to the fundamental order of the operations that are listed earlier in this section, the organization may implement the new record by using a controlled and tested way to prevent outages of the Autodiscover service. To resolve this issue, follow these steps:
-
Create a new SRV record. The SRV record should be created in the DNS zone that matches the user's SMTP domain. The SRV record should have the following properties:
-
Service: _autodiscover
-
Protocol: _tcp
-
Port: 443
-
Host: URL for redirection. This URL may be the Outlook Web Access (OWA) URL because the resolved IP should be the same as the Autodiscover service. Additionally, this may vary from deployment to deployment.
-
-
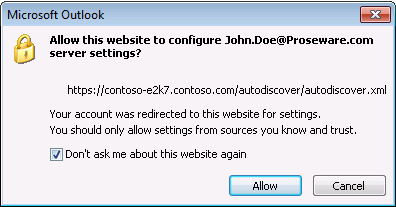
Before you remove the existing A record, the new SRV record should be tested by changing a user's host file to redirect the current A record to an invalid IP. This test can verify that the new SRV record is working as expected before you deploy the new DNS records to the whole organization. Note When the SRV record is used by an Outlook client, the user may receive the following message that advises the user of the redirection that is about to occur. We recommend that the user select the Don't ask me about this website again check box so that the message is not displayed again.
-
When the SRV record works as expected, you can remove the existing A record from DNS.
More Information
For more information about the Autodiscover service, go to the following Microsoft TechNet website: