Introduction
After installing Windows updates released on or after April 14, 2026, certain third-party backup applications that rely on the kernel driver psmounterex.sys might experience failures when attempting to mount or manage disk images. These Windows updates include routine security hardening to help protect devices by blocking third-party drivers with known vulnerabilities. For more information on the psmounterex.sys driver vulnerability, see CVE-2023-43896. Learn about these protections at Microsoft vulnerable driver blocklist.
What new behavior should I expect?
Users and IT administrators might observe the following behavior after installing the update:
-
Backup applications that rely on the kernel driver psmounterex.sys might fail to mount backup image files as virtual drives.
-
Attempting to browse or restore from a backup image might result in errors or timeouts.
-
Failures might be followed by error messages, such as "The backup has failed because Microsoft VSS has timed out during the snapshot creation" or VSS_E_BAD_STATE.
-
Event Viewer might show Code Integrity errors indicating that psmounterex.sys was blocked from loading.
-
Backup creation (full image backups) may still succeed, but image-mount operations will fail.
What caused this change of behavior?
This intentional change of behavior is designed to protect devices against known vulnerabilities in the psmounterex.sys kernel driver. Following the installation of Windows updates released on or after April 14, 2026, Windows Code Integrity enforcement will block vulnerable versions of this driver from loading when the Microsoft vulnerable driver blocklist is enabled.
What should I expect going forward?
The psmounterex.sys driver will remain on the Microsoft vulnerable driver blocklist. Applications that depend on this driver will continue to experience failures until they are updated to a newer version that includes the required protections.
If your backup software relies on this driver, update your backup software. Contact your application vendor if you are unsure whether your version is affected.
How do I determine if a driver is being blocked by the Microsoft vulnerable driver blocklist?
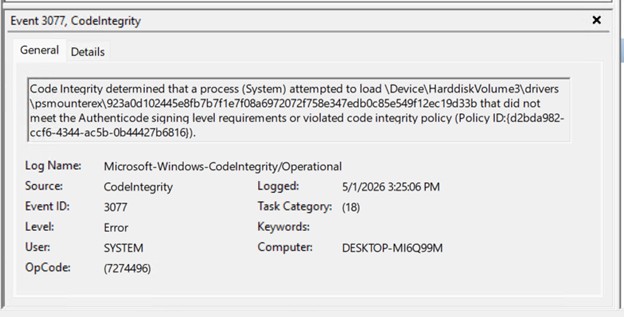
If customers suspect that a driver is being blocked by the Microsoft vulnerable driver blocklist, they can confirm by checking for Event ID 3077 in the Code Integrity Operational log. This event indicates that the driver was blocked in enforcement mode and will include Policy ID {D2BDA982-CCF6-4344-AC5B-0B44427B6816}. To view the event:
-
Right-click Start, and then select Event Viewer.
-
On the left pane, go to Applications and Service Logs\Microsoft\Windows\CodeIntegrity\Operational.
-
On the middle pane, look for Event ID 3077.
Is there additional help for organizations and IT admins?
If your organization needs immediate help managing this change, please contact Microsoft Support for business.










