Information Rights Management (IRM) helps you prevent sensitive information from improper use by unauthorized users. The custom permissions feature allows you to choose who can view, edit, or fully control a file. If your organization has sensitivity labels enabled, defining custom permissions may be required when certain sensitivity labels are applied.
Notes:
-
IRM permissions are different from SharePoint permissions. When applying custom permissions to a file stored in SharePoint, make sure that the users to whom you're assigning IRM permissions also have SharePoint permissions to access the file. To learn more about SharePoint permissions see Share SharePoint files or folders
View content with custom permissions
To view content that has custom permissions, just open the document in the relevant M365 app.
The first time you try to open a document with restricted permissions, you must connect to a licensing server to verify your credentials and obtain a use license. The use license defines the level of access that you have to a file. This process is required for each file that has restricted permission. If you do not have authorization to view the file, you will get an access denial error when attempting to open it.
Apply custom permissions
Currently, applying custom permissions is supported on Microsoft 365 for Windows, Mac, and the web. You can still view content with custom permissions on mobile platforms, but you can’t view or modify the permissions.
Restrict permission to content in files
The custom permissions dialog will open when a sensitivity label that requires custom permissions is applied.
To apply custom permissions without a sensitivity label, select File > Info > Protect Document > Restrict Access > Restricted Access.
Note: If your organization has sensitivity labels enabled, you will be required to select a sensitivity label to restrict permissions.
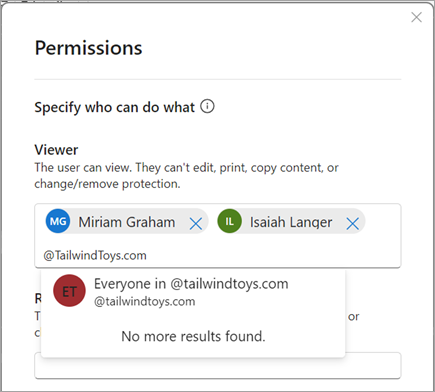
To apply restrictions on a per-user or per-group basis, type a name or email address to search for and select the user or group.
To apply restrictions on a per-organization basis, type @ followed by the domain.
Important Considerations when granting permissions by domain
If you specify a domain to grant permissions to, you're granting those permissions to all of the accounts in that organization.
That means if that organization has other domain names in their Microsoft Entra ID, these permissions also extend to those users. For example, if Tailwind Toys also owns the contosogames.com domain in their Microsoft Entra ID then all the users of contosogames.com would also gain the permissions granted to tailwindtoys.com users.
This is also true of subdomains. Granting permissions to sales.tailwindtoys.com also grants those permissions to all of the other accounts in tailwindtoys.com, as well as any other domains they may have in their Microsoft Entra ID.
Specifying who can do what with the file
Permissions levels are pre-defined groups of usage rights that give users different permissions within the file. The four permissions levels available in M365 for Windows are:
-
Viewer: The user can view, but they can't edit, print, copy content, or change/remove protection.
-
Restricted Editor: The user can view and edit, but they can't print, copy content, or change/remove protection.
-
Editor: The user can view, edit, print, and copy content, but they can't change/remove protection.
-
Owner: The user has full control over the file, including the ability to change/remove protection.
Setting more options
You can optionally specify additional settings when applying custom permissions.
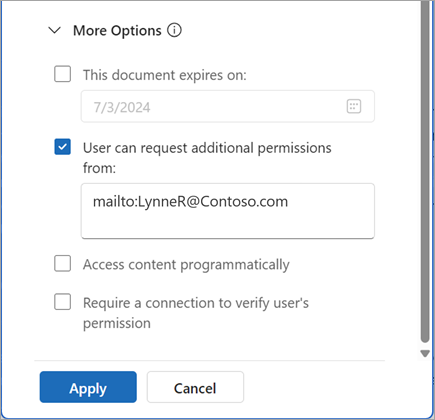
You can specify a date on which the permissions you are granting should expire.
-
In the More Options section of the Permissions dialog, select the 'This document expires on' checkbox.
-
Use the date picker to select an expiration date. Note that the date selected must be in the future.
When a user opens a file that they do not have full permissions for, they are offered the option to contact the file owner to request additional permissions. By default, the primary owner of the file is the contact for this request. You can choose to define another point of contact for requesting additional permissions.
Note: Users can only change permissions on a file if they are an Owner
By default, file content protected with user-defined permissions cannot be accessed programmatically. To allow programmatic access of file content, select Access content programmatically in the More Options section of the Permissions dialog.
The first time a user opens a file with restricted permissions in M365 for Windows or Mac, a use license for the file is granted to the user by the licensing server. The use license is a certificate that contains the user’s usage rights for the file as well as the encryption key used to encrypt the file. Once granted, the use license is valid for 30 days or until the custom expiration date, whichever comes first. During this period, the user is not reauthenticated or reauthorized to access the file using the same device. This means that even if the user’s permission to the file is changed or removed, they will still be able to access the file until the previously granted use license expires.
To require the user’s permission to the file to be verified each time they open it, select Require a connection to verify user’s permission in the More Options section of the Permissions dialog.
Restrict permission to content in files
The custom permissions dialog will open when a sensitivity label that requires custom permissions is applied.
To apply custom permissions without a sensitivity label, select File > Restrict Permissions > Restricted Access...
Note: If your organization has sensitivity labels enabled, you will be required to select a sensitivity label to restrict permissions.
To apply restrictions on a per-user basis, type a name or email address to search and select the user. If you need to apply restrictions on a per-organization basis, use Office on the web.
Specifying who can do what with the file
Permissions levels are pre-defined groups of usage rights that give users different permissions within the file. The three permissions levels available in M365 for Mac are:
-
Read: The user can view, but they can’t edit, print, copy content, or change/remove protection.
-
Change: The user can view, edit, and copy content, but they can’t print or change/remove protection.
-
Full Control: The user has full control over the document, including the ability to change/remove protection.
Setting more options
You can optionally specify additional settings when applying custom permissions.
You can specify a date on which the permissions you are granting should expire.
-
In the More Options section of the Set Permissions dialog, select the This document expires on' checkbox.
-
Use the date picker to select an expiration date. Note that the date selected must be in the future.
You can grant users with Read or Change permissions the ability to print content.
In the More Options section of the Set Permissions dialog, select Allow people with Change or Read permission to print content.
You can grant users with Read permission the ability to copy content.
In the More Options section of the Set Permissions dialog, select Allow people with Read permission to copy content.
By default, file content protected with custom permissions can be accessed programmatically. To disallow programmatic access of file content, deselect Access content programmatically in the More Options section of the Set Permissions dialog.
The first time a user opens a file with restricted permissions in M365 for Windows or Mac, a use license for the file is granted to the user by the licensing server. The use license is a certificate that contains the user’s usage rights for the file as well as the encryption key used to encrypt the file. Once granted, the use license is valid for 30 days or until the custom expiration date, whichever comes first. During this period, the user is not reauthenticated or reauthorized to access the file using the same device. This means that even if the user’s permission to the file is changed or removed, they will still be able to access the file until the previously granted use license expires.
To require the user’s permission to the file to be verified each time they open it, select the ‘Require a connection to verify permissions’ checkbox in the More Options section of the Set Permissions dialog.
Restrict permission to content in files
The custom permissions dialog will open when a sensitivity label that requires custom permissions is applied.
To apply restrictions on a per-user or per-group basis, type a name or email address to search for and select the user or group.
To apply restrictions on a per-organization basis, type @ followed by the domain.
Important Considerations when granting permissions by domain
If you specify a domain to grant permissions to, you're granting those permissions to all of the accounts in that organization.
That means if that organization has other domain names in their Microsoft Entra ID, these permissions also extend to those users. For example, if Tailwind Toys also owns the contosogames.com domain in their Microsoft Entra ID then all the users of contosogames.com would also gain the permissions granted to tailwindtoys.com users.
This is also true of subdomains. Granting permissions to sales.tailwindtoys.com also grants those permissions to all of the other accounts in tailwindtoys.com, as well as any other domains they may have in their Microsoft Entra ID.
Specifying who can do what with the file
Permissions levels are pre-defined groups of usage rights that give users different permissions within the file. The four permissions levels available in M365 for Windows are:
-
Viewer: The user can view, but they can't edit, print, copy content, or change/remove protection.
-
Restricted Editor: The user can view and edit, but they can't print, copy content, or change/remove protection.
-
Editor: The user can view, edit, print, and copy content, but they can't change/remove protection.
-
Owner: The user has full control over the file, including the ability to change/remove protection.
Setting more options
You can optionally specify additional settings when applying custom permissions.
When a user opens a file that they do not have full permissions for, they are offered the option to contact the file owner to request additional permissions. By default, the primary owner of the file is the contact for this request. You can choose to define another point of contact for requesting additional permissions.
Note: Users can only change permissions on a file if they are an Owner
By default, file content protected with user-defined permissions cannot be accessed programmatically. To allow programmatic access of file content, select Access content programmatically in the More Options section of the Permissions dialog.
The first time a user opens a file with restricted permissions in M365 for Windows or Mac, a use license for the file is granted to the user by the licensing server. The use license is a certificate that contains the user’s usage rights for the file as well as the encryption key used to encrypt the file. Once granted, the use license is valid for 30 days or until the custom expiration date, whichever comes first. During this period, the user is not reauthenticated or reauthorized to access the file using the same device. This means that even if the user’s permission to the file is changed or removed, they will still be able to access the file until the previously granted use license expires.
To require the user’s permission to the file to be verified each time they open it, select Require a connection to verify user’s permission in the More Options section of the Permissions dialog.
What IRM does
Information Rights Management (IRM) helps do the following:
-
Prevent an authorized user from editing, copying, or printing restricted content
-
Protect content wherever it is sent and enforce organizational policies that govern the use and sharing of content within the organization
-
Provide file expiration, so that content in a file can no longer be viewed after a specified time
-
Prevent programmatic access to file content
IRM can’t prevent restricted content from being:
-
Copied using third-party screen-capture software
-
Digitally photographed, hand-copied, or re-typed by an authorized user
-
Erased or corrupted by malicious software