Sample Secure Boot E2E Automation Guide
Applies To
Original publish date: March 16, 2026Last date updated: April 3, 2026KB ID: 5084567
In this article
Overview
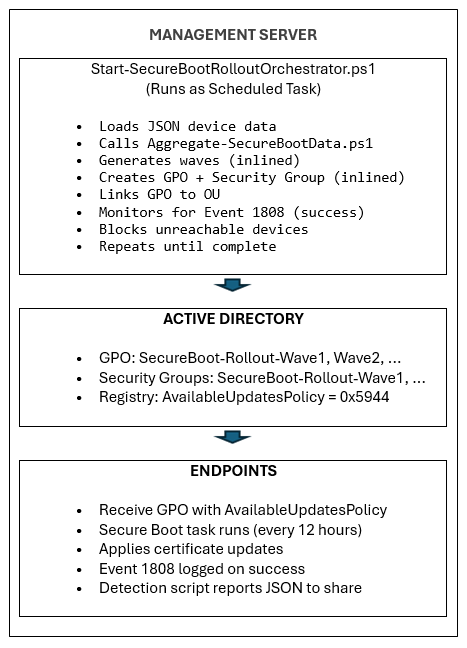
This guide describes the automated deployment system for Windows Secure Boot DB certificate updates using Group Policy and progressive rollout waves.
The Secure Boot Certificate Rollout Automation is a PowerShell-based system that deploys Windows Secure Boot DB certificate updates to domain-joined machines in a controlled, graduated manner.
Key Features
|
Feature |
Description |
|
Graduated Rollout |
1 > 2 > 4 > 8… devices per bucket |
|
Automatic Blocking |
Buckets with unreachable devices are excluded |
|
Automated GPO Deployment |
Single orchestrator script handles everything |
|
Scheduled Task Execution |
No interactive prompts required |
|
Real-time Monitoring |
Status viewer with progress bar |
Certificate Updates Settings Reference
In this section
AvailableUpdatesPolicy Group policy
|
Registry location |
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecureBoot |
|
Name |
AvailableUpdatesPolicy |
|
Value |
0x5944 (DWORD) |
This is the GPO/ADMX-controlled key that:
-
Persists across reboots
-
Is set by Group Policy / MDM
-
Does not cause retry loops (cleared via ClearRolloutFlags)
-
Is the correct key for policy-driven deployment
Reference: Group Policy Objects (GPO) method of Secure Boot for Windows devices with IT-managed updates
WinCSFlags - Windows Configuration System Flags
Domain administrators can alternatively use the Windows Configuration System (WinCS) released with Windows OS updates to deploy the Secure Boot updates across domain-joined Windows clients and servers. It consists of a command-line interface (CLI) utility to query and apply Secure Boot configurations locally to a machine.
|
Feature name |
WinCS Key |
Description |
|
Feature_AllKeysAndBootMgrByWinCS |
F33E0C8E002 |
Enabling this key allows installation of the following Microsoft-provided Secure Boot new certificates on your device.
|
Reference: Windows Configuration System (WinCS) APIs for Secure Boot
Architecture
Phase 1: Detection and Status Monitoring at Enterprise level
In this section
Scripts needed for Phase 1
Sample Secure Boot Inventory Data Collection scripts
|
Sample Script Name |
Purpose |
Runs On |
|
Collects device status data |
Each endpoint (via GPO) |
|
|
Generates reports and dashboards |
Admin workstation |
|
|
Automates GPO creation for data collection |
Domain Controller |
back to "Phase 1: Detection and Status Monitoring at Enterprise level"
Local Testing
Before deploying via GPO, test the collection script on a single machine to verify functionality.
-
Run Collection Script Locally Open an elevated PowerShell prompt and execute:
& .\Detect-SecureBootCertUpdateStatus.ps1 -OutputPath "C:\Temp\SecureBootTest"
-
Verify JSON Output
# View the collected data Get-Content "C:\Temp\SecureBootTest\*_latest.json" | ConvertFrom-Json | Format-List
Key Fields to Verify • SecureBootEnabled – Should be True or False • OverallStatus – Complete, ReadyForUpdate, NeedsData, or Error • BucketHash – Device bucket for confidence data matching • SecureBootTaskEnabled - Shows status of Secure Boot Update Task.
-
Test Aggregation Script
# Generate reports from collected data & ".\Aggregate-SecureBootData.ps1" ` -InputPath "C:\Temp\SecureBootTest" ` -OutputPath "C:\Temp\SecureBootReports" # Open the HTML dashboard Start-Process "C:\Temp\SecureBootReports\SecureBoot_Dashboard_*.html"
back to "Phase 1: Detection and Status Monitoring at Enterprise level"
GPO Deployment
Use the automation script provided from a domain controller:
# Run on Domain Controller as Domain Admin for interactive OU Section – Recommended # Replace the “Contoso.com”, “Contoso” with the name of the domain # Replace FILESERVER with the file server name. Script shows list of OUs to deploy GPO on .\Deploy-GPO-SecureBootCollection.ps1 ` -DomainName "contoso.com" ` -AutoDetectOU ` -CollectionSharePath "\\FILESERVER\SecureBootData$" -ScriptSourcePath ".\Detect-SecureBootCertUpdateStatus.ps1" ` -Schedule "Daily" ` -ScheduleTime "14:00" ` -RandomDelayHours 4
This script will perform the following:
-
Creates new GPO with specified name
-
Copies collection script to SYSVOL for high availability
-
Configures Computer Startup Script
-
Links GPO to target OU
-
Optionally creates scheduled task for periodic collection
The following table provides guidance in how long the delay will be based on your fleet size.
|
Fleet size |
Delay range |
|
1-10K devices |
4 hours |
|
10K-50K devices |
8 hours |
|
50K+ devices |
12-24 hours |
back to "Phase 1: Detection and Status Monitoring at Enterprise level"
GPO Settings Summary
|
Setting |
Location |
Value |
|
Startup Script |
Computer Config → Scripts |
Detect-SecureBootCertUpdateStatus.ps1 |
|
Script Parameters |
(same) |
-OutputPath "\\server\share$" |
|
Execution Policy |
Computer Config → Admin Templates → PowerShell |
Allow local and remote signed |
|
Scheduled Task |
Computer Config → Preferences → Scheduled Tasks |
Daily/Weekly collection |
back to "Phase 1: Detection and Status Monitoring at Enterprise level"
Verification
-
Force GPO Update on Test Machine
## On a test workstation gpupdate /force # Reboot the client machines to startup script or it will trigger on next schedule. Restart-Computer -Force
-
Verify Data Collection
# Check if data was collected (on file server or from any machine) Get-ChildItem "\\fileserver\SecureBootData$" | Sort-Object LastWriteTime -Descending | Select-Object -First 10 # Verify JSON content Get-Content "\\fileserver\SecureBootData$\TESTPC_latest.json" | ConvertFrom-Json
-
Check GPO Application
# Verify GPO is applied to the computer Select-String "SecureBoot" The script also saves a local copy for redundancy: Get-ChildItem "C:\ProgramData\SecureBootCollection\"
back to "Phase 1: Detection and Status Monitoring at Enterprise level"
Phase 2: Secure Boot Certificate Update Orchestration Scripts
Important: Ensure Phase1 is completed including data collection on each end point to remote server shares.
In this section
Scripts needed for Phase 2
Sample Secure Boot Inventory Data Collection scripts
|
Sample script name |
Purpose |
Runs on |
|
Collects device status data |
Each endpoint (via GPO) |
|
|
Generates reports and dashboards |
Admin workstation |
|
|
Automates GPO creation for data collection |
Domain Controller |
|
|
Fully automated, continuous orchestration with automated GPO deployment for certificate installation |
Admin workstation |
|
|
Deploys Orchestrator script as scheduled task for automated rollout |
Domain Controller |
|
|
View Secure Boot Certificate Roll out status from any workstation |
Admin Workstation |
|
|
Enables Secure Boot Update Task |
On End points where task is disabled (Run only once to enable the task if disabled) |
back to "Phase 2: Secure Boot Certificate Update Orchestration Scripts"
Start-SecureBootRolloutOrchestrator.ps1
-
Purpose: Fully automated, continuous orchestration with automated GPO deployment.
-
What it does
-
Calls Aggregate-SecureBootData.ps1 for device status
-
Generates rollout waves using progressive doubling
-
Creates GPO for certificate deployment using one of following methods
-
Secure boot Group policy AvailableUpdatesPolicy = 0x5944 (Default)
-
WinCS method (Parameter –UseWinCS)
-
-
Creates AD security groups for targeting
-
Adds computer accounts to security groups
-
Configures GPO security filtering
-
Links GPO to target OU
-
Monitors for blocked buckets (unreachable devices)
-
Auto-unblocks when devices recover
-
-
Usage
# Interactive (testing) .\Start-SecureBootRolloutOrchestrator.ps1 ` -AggregationInputPath "\\fileserver\SecureBootData$" ` -ReportBasePath "C:\SecureBootReports" ` -PollIntervalMinutes 30
# Interactive (testing), leveraging WinCS method .\Start-SecureBootRolloutOrchestrator.ps1 ` -AggregationInputPath "\\fileserver\SecureBootData$" ` -ReportBasePath "C:\SecureBootReports" ` -PollIntervalMinutes 30 ` -UseWinCS
-
Admin commands
# List blocked buckets .\Start-SecureBootRolloutOrchestrator.ps1 -ReportBasePath "C:\SecureBootReports" -ListBlockedBuckets
# Unblock specific bucket .\Start-SecureBootRolloutOrchestrator.ps1 -ReportBasePath "C:\SecureBootReports" -UnblockBucket "Dell|Latitude5520|BIOS1.2"
# Unblock all .\Start-SecureBootRolloutOrchestrator.ps1 -ReportBasePath "C:\SecureBootReports" -UnblockAll
-
Parameters
Parameter
Default
Description
AggregationInputPath
Required
UNC path to endpoint JSON files
ReportBasePath
Required
Local path for reports and state
TargetOU
Domain root
OU to link GPOs
WavePrefix
SecureBoot-Rollout
GPO/group naming prefix
MaxWaitHours
72
Hours before checking device reachability
PollIntervalMinutes
1440
Minutes between status checks
DryRun
False
Show what would happen without changes
Note on PollIntervalMinutes: When running the orchestrator directly, the default is 1440 minutes (24 hours). When deployed via Deploy-OrchestratorTask.ps1, the default is 30 minutes. The deploy script passes its own default to the orchestrator. Use 30 minutes for active rollout, 1440 for maintenance monitoring.
Optional Parameters
Parameter
Default
Description
UseWinCS
False
Use WinCS method instead of AvailableUpdatesPolicy GPO
WinCSKey
F33E0C8E002
WinCS key for Secure Boot configuration
AllowListPath
(none)
Path to file with hostnames to ALLOW for targeted/pilot rollout. Supports .txt or .csv.
AllowADGroup
(none)
AD security group of computer accounts to ALLOW. Example: "SecureBoot-Pilot-Computers"
ExclusionListPath
(none)
Path to file with hostnames to EXCLUDE from rollout (VIP/executive devices)
ExcludeADGroup
(none)
AD security group of computer accounts to exclude. Example: "VIP-Computers"
ListBlockedBuckets
False
Display currently blocked device buckets
UnblockBucket
(none)
Unblock a specific bucket. Format: "Manufacturer|Model|BIOS"
UnblockAll
False
Unblock all blocked device buckets
back to "Phase 2: Secure Boot Certificate Update Orchestration Scripts"
Deploy-OrchestratorTask.ps1
-
Purpose: Deploys the orchestrator as a Windows Scheduled Task.
-
Benefits
-
No PowerShell security prompts (ExecutionPolicy Bypass)
-
Runs in background continuously
-
No user interaction required
-
Survives reboots
-
-
Usage
-
Deploy with domain service account (recommended)
-
Use AvailableUpdates Group Policy (Default Method)
.\Deploy-OrchestratorTask.ps1 ` -AggregationInputPath "\\server\SecureBootData$" ` -ReportBasePath "C:\SecureBootReports" ` -ServiceAccount "DOMAIN\svc_secureboot"
-
Use WinCS method
.\Deploy-OrchestratorTask.ps1 ` -AggregationInputPath "\\server\SecureBootData$" ` -ReportBasePath "C:\SecureBootReports" ` -ServiceAccount "DOMAIN\svc_secureboot" -UseWinCS
-
-
Deploy with SYSTEM account
-
Use AvailableUpdates Group Policy (Default Method)
.\Deploy-OrchestratorTask.ps1 ` -AggregationInputPath "\\server\SecureBootData$" ` -ReportBasePath "C:\SecureBootReports"
-
Use WinCS method.\Deploy-OrchestratorTask.ps1
-AggregationInputPath "\\server\SecureBootData$" ` -ReportBasePath "C:\SecureBootReports" -UseWinCS
-
Service Account Requirements
-
Domain Admin (for New-GPO, New-ADGroup, Add-ADGroupMember)
-
Read access to JSON file share
-
Write access to ReportBasePath
-
-
-
back to "Phase 2: Secure Boot Certificate Update Orchestration Scripts"
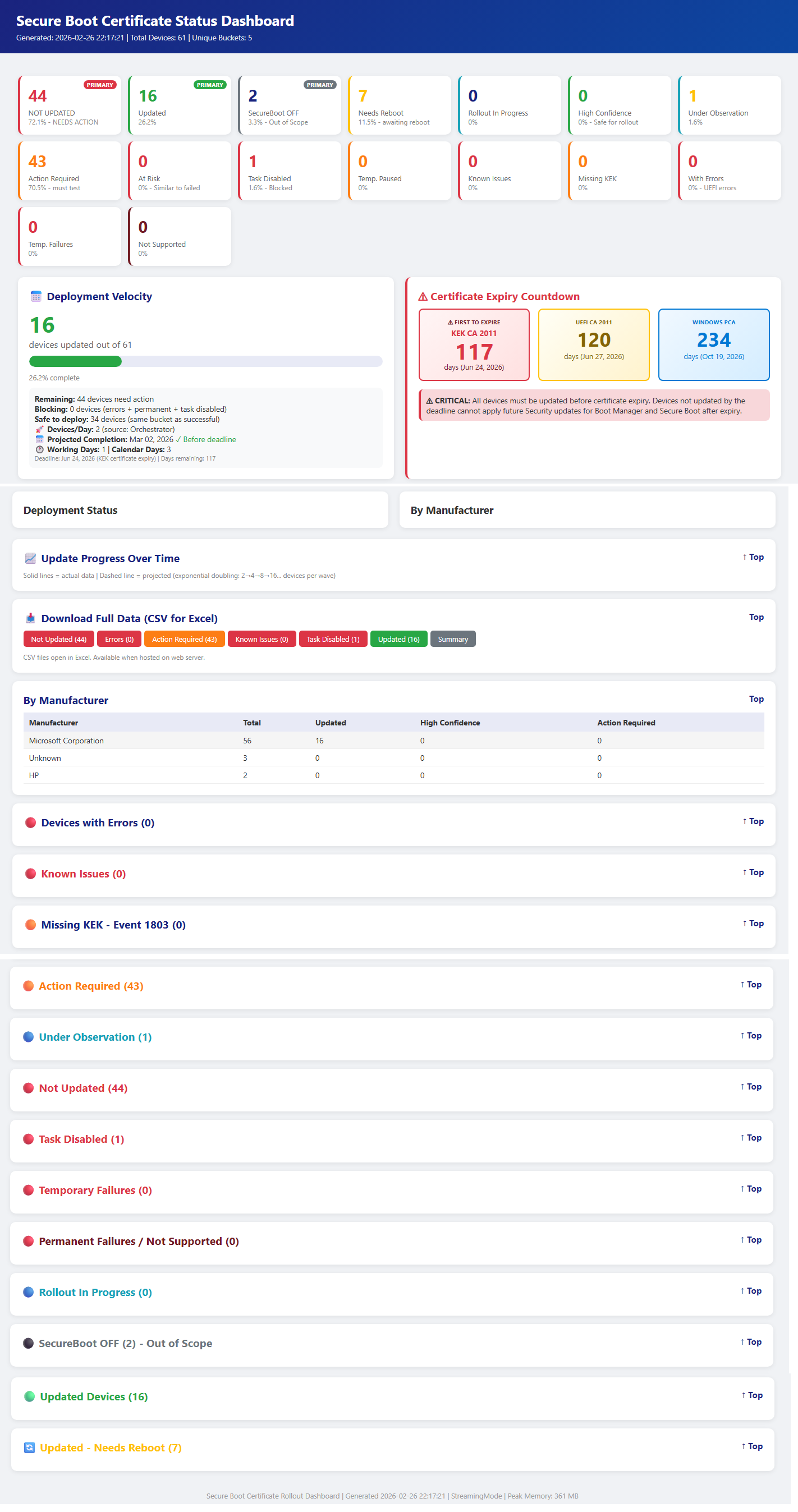
Get-SecureBootRolloutStatus.ps1
-
Purpose: View rollout progress from any workstation.
-
What it shows
-
Scheduled task state (Running/Ready/Stopped)
-
Current wave number
-
Devices targeted vs updated
-
Visual progress bar
-
Blocked buckets summary
-
Link to latest HTML dashboard
-
-
Usage
# Quick status check .\Get-SecureBootRolloutStatus.ps1 -ReportBasePath "C:\SecureBootReports"
# Continuous monitoring (refreshes every 30 seconds) .\Get-SecureBootRolloutStatus.ps1 -ReportBasePath "C:\SecureBootReports" -Watch 30
# View blocked buckets .\Get-SecureBootRolloutStatus.ps1 -ReportBasePath "C:\SecureBootReports" -ShowBlocked
# View wave history .\Get-SecureBootRolloutStatus.ps1 -ReportBasePath "C:\SecureBootReports" -ShowWaves
# View recent log .\Get-SecureBootRolloutStatus.ps1 -ReportBasePath "C:\SecureBootReports" -ShowLog
# Open dashboard in browser .\Get-SecureBootRolloutStatus.ps1 -ReportBasePath "C:\SecureBootReports" -OpenDashboard
-
Parameters
Parameter
Required?
Default
Description
ReportBasePath
Required
—
Local path to reports and state files
ShowLog
Optional
False
Display recent orchestrator log entries
ShowBlocked
Optional
False
Display blocked buckets details
ShowWaves
Optional
False
Display wave history
Watch
Optional
0 (disabled)
Auto-refresh interval in seconds. Example: -Watch 30 refreshes every 30 seconds.
OpenDashboard
Optional
False
Open the latest HTML dashboard in the default browser
-
Sample output
============================================================== SECURE BOOT ROLLOUT STATUS 2026-02-17 19:30:00 ======================================================
Scheduled Task: Running
ROLLOUT PROGRESS ---------------------------------------- Status: InProgress Current Wave: 5 Total Targeted: 1250 Total Updated: 847
Progress: [█████████████████████░░░░░░░░░░░░░░░░░░░] 67.8%
BLOCKED BUCKETS: 2 buckets need attention Run with -ShowBlocked for details
LATEST DASHBOARD C:\SecureBootReports\Aggregation_20260217_193000\SecureBoot_Dashboard.html __________________________________________________________________________________________
back to "Phase 2: Secure Boot Certificate Update Orchestration Scripts"
E2E Deployment Steps (Quick Reference Guide)
In this section
Phase 1: Detection Infrastructure
-
Step 1: Create Collection Share
# On file server $sharePath = "D:\SecureBootData" New-Item -ItemType Directory -Path $sharePath -Force New-SmbShare -Name "SecureBootData$" -Path $sharePath -FullAccess "Domain Admins" -ChangeAccess "Domain Computers"
# Set NTFS permissions $acl = Get-Acl $sharePath $rule = New-Object System.Security.AccessControl.FileSystemAccessRule("Domain Computers","Modify","Allow") $acl.AddAccessRule($rule) Set-Acl $sharePath $acl
-
Step 2: Deploy Detection GPO
.\Deploy-GPO-SecureBootCollection.ps1 ` -DomainName "contoso.com" ` -OUPath "OU=Workstations,DC=contoso,DC=com" ` -CollectionSharePath "\\server\SecureBootData$"
-
Step 3: Wait for Endpoints to Report (24-48 hours)
# Check collection progress (Get-ChildItem "\\server\SecureBootData$" -Filter "*.json").Count
Phase 2: Orchestrated Rollout
-
Step 4: Prerequisites Check
-
Detection GPO deployed (Step 2)
-
At least 50+ endpoints reporting JSON
-
Service account with Domain Admin rights
-
Management server with PowerShell 5.1+
-
-
Step 5: Deploy Orchestrator as Scheduled Task
.\Deploy-OrchestratorTask.ps1 ` -AggregationInputPath "\\server\SecureBootData$" ` -ReportBasePath "C:\SecureBootReports" ` -ServiceAccount "DOMAIN\svc_secureboot"
-
Step 6: Monitor Progress
.\Get-SecureBootRolloutStatus.ps1 -ReportBasePath "C:\SecureBootReports"
-
Step 7: View Dashboard
.\Get-SecureBootRolloutStatus.ps1 -ReportBasePath "C:\SecureBootReports" -OpenDashboard
-
Step 8: Manage Blocked Buckets
# List blocked .\Start-SecureBootRolloutOrchestrator.ps1 -ReportBasePath "C:\SecureBootReports" -ListBlockedBuckets
# Investigate and unblock .\Start-SecureBootRolloutOrchestrator.ps1 -ReportBasePath "C:\SecureBootReports" -UnblockBucket "Manufacturer|Model|BIOS"
-
Step 9: Verify Completion
.\Get-SecureBootRolloutStatus.ps1 -ReportBasePath "C:\SecureBootReports" # Status should show "Completed"
State Files
The orchestrator maintains state in ReportBasePath\RolloutState\:
|
File |
Description |
|
RolloutState.json |
Wave history, targeted devices, status |
|
BlockedBuckets.json |
Buckets needing investigation |
|
DeviceHistory.json |
Device tracking by hostname |
|
Orchestrator_YYYYMMDD.log |
Daily activity logs |
Troubleshooting
In this section
Orchestrator Not Progressing
-
Check scheduled task
Get-ScheduledTask -TaskName "SecureBoot-Rollout-Orchestrator"
-
Check logs
Get-Content "C:\SecureBootReports\RolloutState\Orchestrator_*.log" -Tail 50
-
Verify JSON data freshness
(Get-ChildItem "\\server\SecureBootData$" -Filter "*.json" | Where-Object { $_.LastWriteTime -gt (Get-Date).AddDays(-1) }).Count
Blocked Buckets
-
List blocked.
.\Start-SecureBootRolloutOrchestrator.ps1 -ReportBasePath "C:\SecureBootReports" -ListBlockedBuckets
-
Investigate device reachability.
-
Check for firmware issues.
-
Unblock after investigation.
GPO Not Applying
-
Verify GPO exists.
Get-GPO -Name "SecureBoot-Rollout-Wave*"
-
Check security filtering.
Get-GPPermission -Name "GPO-Name" -All
-
Verify computer is in security group.
-
Apply the GPO on the target.
gpupdate /force
back to "Troubleshooting"