Device Security in the Windows Security App
Applies To
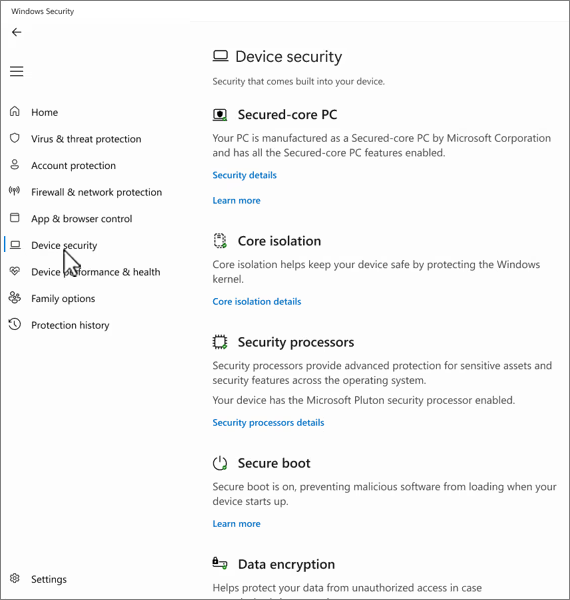
The Device security page in the Windows Security app helps protect your Windows device by managing hardware‑based and operating system security features, including Secure Boot, core isolation, and processor‑level protections. These features work together to defend against malware, firmware attacks, and system compromise. The page is divided into the following sections:
-
Secured-core PC: If your device is a Secured-core PC, it shows information about the Secured-core PC features
-
Core isolation: Here you can configure security features that protect the Windows kernel
-
Security processor: Provides information about the security processor, which is call the trusted platform module (TPM)
-
Secure boot: If secure boot is enabled, you can find more information about it
-
Data encryption: Here you can find a link to Windows Settings, where you can configure device encryption and other BitLocker settings
-
Hardware security capability: Assesses your device's hardware security features
In the Windows Security app on your PC, select Device security, or use the following shortcut:
Secured-core PC
A Secured-core PC is designed to provide advanced security features right out of the box. These PCs integrate hardware, firmware, and software to offer robust protection against sophisticated threats.
In the Windows Security app on your PC, select Device security > Security details.
For more information, see Windows 11 Secured-core PCs.
Core isolation
Core isolation provides security features designed to protect core processes of Windows from malicious software by isolating them in memory. It does this by running those core processes in a virtualized environment.
In the Windows Security app on your PC, select Device security > Core isolation details or use the following shortcut:
Note: the features exposed on the core isolation page vary depending on what version of Windows you're running, and the hardware components installed.
Memory integrity, also known as Hypervisor-protected Code Integrity (HVCI) is a Windows security feature that makes it difficult for malicious programs to use low-level drivers to hijack your PC.
A driver is a piece of software that lets the operating system (Windows in this case) and a device (like a keyboard or a webcam) talk to each other. When the device wants Windows to do something, it uses the driver to send that request.
Memory integrity works by creating an isolated environment using hardware virtualization.
Think of it like a security guard inside a locked booth. This isolated environment (the locked booth in our analogy) prevents the memory integrity feature from being tampered with by an attacker. A program that wants to run a piece of code which may be dangerous has to pass the code to memory integrity inside that virtual booth so that it can be verified. When memory integrity is comfortable that the code is safe it hands the code back to Windows to run. Typically, this happens very quickly.
Without memory integrity running, the security guard stands right out in the open where it's much easier for an attacker to interfere with or sabotage the guard, making it easier for malicious code to sneak past and cause problems.
You can turn memory integrity On or Off using the toggle button.
Note: To use memory integrity, you must have hardware virtualization enabled in your system’s UEFI or BIOS.
What if it says I have an incompatible driver?
If memory integrity fails to turn on, it may tell you that you have an incompatible device driver already installed. Check with the manufacturer of the device to see if they have an updated driver available. If they don’t have compatible driver available, you might be able to remove the device or app that uses that incompatible driver.
Note: If you try to install a device with an incompatible driver after turning on memory integrity, you might receive the same message. If so, the same advice applies - check with the device manufacturer to see if they have an updated driver you can download, or don’t install that particular device until a compatible driver is available.
Hardware enforced stack protection is a hardware-based security feature that makes it difficult for malicious programs to use low-level drivers to hijack your PC.
A driver is a piece of software that lets the operating system (Windows in this case) and a device (like a keyboard or a webcam) talk to each other. When the device wants Windows to do something, it uses the driver to send that request.
Hardware enforced stack protection works by preventing attacks that modify return addresses in kernel-mode memory to launch malicious code. This security feature requires a CPU that contains the ability to verify the return addresses of running code.
When executing code in kernel-mode, return addresses on the kernel-mode stack can be corrupted by malicious programs or drivers in order to redirect normal code execution to malicious code. On supported CPUs, the CPU maintains a second copy of valid return addresses on a read-only shadow stack that drivers cannot modify. If a return address on the regular stack has been modified, the CPU can detect this discrepancy by checking the copy of the return address on the shadow stack. When this discrepancy occurs, the computer prompts a stop error, sometimes known as a blue screen, to prevent the malicious code from executing.
Not all drivers are compatible with this security feature, as a small number of legitimate drivers engage in return address modification for non-malicious purposes. Microsoft has been engaging with numerous driver publishers to ensure that their latest drivers are compatible with hardware enforced stack protection.
You can turn hardware enforced stack protection On or Off using the toggle button.
To use hardware enforced stack protection, you must have memory integrity enabled, and you must be running a CPU that supports Intel Control-Flow Enforcement Technology or AMD Shadow Stack.
What if it says I have an incompatible driver or service?
If hardware enforced stack protection fails to turn on, it might tell you that you have an incompatible device driver or service already installed. Check with the manufacturer of the device or the application publisher to see if they have an updated driver available. If they don’t have a compatible driver available, you might be able to remove the device or app that uses that incompatible driver.
Some applications might install a service instead of a driver during the application's installation and install the driver only when the application is launched. For more accurate detection of incompatible drivers, services that are known to be associated with incompatible drivers are also enumerated.
Note: If you try to install a device or app with an incompatible driver after turning on hardware enforced stack protection, you may see the same message. If so, the same advice applies - check with the device manufacturer or app publisher to see if they have an updated driver you can download, or don’t install that particular device or app until a compatible driver is available.
Also known as Kernel DMA protection this security feature protects your device against attacks that can occur when a malicious device is plugged into a Peripheral Component Interconnect (PCI) port like a Thunderbolt port.
A simple example of one of these attacks would be if someone leaves their PC for a quick coffee break, and while they were away, an attacker steps in, plugs in a USB-like device and walks away with sensitive data from the machine, or injects malware that allows them to control the PC remotely.
Memory access protection prevents these kinds of attacks by denying direct access to the memory to those devices except under special circumstances, particularly when the PC is locked, or the user is signed out.
Tip: For more information, see Kernel DMA Protection.
Every device has some software that's been written to the read-only memory of the device - basically written to a chip on the system board - that is used for the basic functions of the device, such as loading the operating system that runs all the apps we're used to using. Since that software is difficult (but not impossible) to modify we refer to it as firmware.
Because the firmware loads first and runs under the operating system, security tools and features that run in the operating system have a difficult time detecting it or defending against it. Like a house that depends on a good foundation to be secure, a computer needs its firmware to be secure in order to ensure that the operating system, applications, and data on that computer are safe.
System Guard is a set of features that helps to ensure that attackers can't get your device to start with untrusted or malicious firmware.
Platforms that offer firmware protection typically also protect the System Management Mode (SMM), a highly privileged operating mode, to varying degrees. You can expect one of the three values, with a higher number indicating a greater degree of SMM protection:
-
Your device meets firmware protection version one: this offers the foundational security mitigations to help SMM resist exploitation by malware, and prevents exfiltration of secrets from the OS (including VBS)
-
Your device meets firmware protection version two: in addition to firmware protection version one, version two ensures that SMM can't disable Virtualization-based Security (VBS) and kernel DMA protections
-
Your device meets firmware protection version three: in addition to firmware protection version two, it further hardens the SMM by preventing access to certain registers that have the ability to compromise the OS (including VBS)
Tip: For more information, see System Guard: How a hardware-based root of trust helps protect Windows
Local Security Authority (LSA) protection is a Windows security feature to help prevent the theft of credentials used for signing into Windows.
The Local Security Authority (LSA) is a crucial process in Windows involved in user authentication. It’s responsible for verifying credentials during the login process and managing authentication tokens and tickets used to enable single sign-on for services. LSA protection helps prevent untrusted software from running inside LSA or from accessing LSA memory.
How do I manage Local Security Authority protection?
You can turn LSA protection On or Off using the toggle button.
After you have changed the setting, you must reboot for it to take effect.
Note: To help keep credentials safe, LSA protection is enabled by default on all devices. For new installs, it is enabled immediately. For upgrades, it is enabled after rebooting after an evaluation period of five days.
What if I have incompatible software?
If LSA protection is enabled and it blocks the loading of software into the LSA service, a notification indicates the blocked file. You might be able to remove the software loading the file, or you can disable future warnings for that file when it’s blocked from loading into LSA.
Note: Credential Guard is available on devices running Enterprise or Education versions of Windows.
While you're using your work or school device it will be quietly signing into and gaining access to a variety of things such as files, printers, apps, and other resources in your organization. Making that process secure, yet easy for the user, means that your PC has a number of authentication tokens on it at any given time.
If an attacker can gain access to one, or more, of those tokens, they might be able to use them to gain access to the organizational resource (sensitive files, etc) that the token is for. Credential Guard helps to protect those tokens by putting them in a protected, virtualized, environment where only certain services can access them when necessary.
Tip: To learn more, see How Credential Guard works.
A driver is a piece of software that lets the operating system (Windows in this case) and a device (like a keyboard or a webcam) talk to each other. When the device wants Windows to do something, it uses the driver to send that request. Because of this, drivers have a lot of sensitive access in your system.
Windows 11 includes a blocklist of drivers that have known security vulnerabilities, have been signed with certificates used to sign malware, or that circumvent the Windows Security Model.
If you have memory integrity, Smart App Control, or Windows S mode on, the vulnerable driver blocklist will be on too.
Note: If you encounter a banner titled Program Compatibility Assistant with a message indicating that a driver cannot load, or that a security setting is preventing a driver from loading, check for updated drivers via Windows Update or through Device Manager. If no updates are available, contact your hardware manufacturer for an updated driver.
Security processor
The Security processor settings under the Device Security page in the Windows Security app provide details about the Trusted Platform Module (TPM) on your device. The TPM is a hardware component designed to enhance security by performing cryptographic operations.
Note: If you don't see a Security processor entry on this screen then it's likely that your device doesn't have the TPM (Trusted Platform Module) hardware necessary for this feature or that it's not enabled in UEFI (Unified Extensible Firmware Interface). Check with your device manufacturer to see if your device supports TPM and, if so, steps to enable it.
This is where you’ll find info about the security processor manufacturer and version numbers, as well as about the security processor’s status.
In the Windows Security app on your PC, select Device security > Security processor details or use the following shortcut:
Security processor details
If your security processor isn't working properly, you can select the Security processor troubleshooting link to see any error messages and advanced options, or use the following shortcut:
Security processor troubleshooting
The security processor troubleshooting page provides any relevant error messages about the TPM. Here's a list of the error messages and details:
|
Message |
Details |
|---|---|
|
A firmware update is needed for your security processor (TPM). |
Your device's motherboard doesn't appear to support TPM currently, but a firmware update might resolve this. Check with your device's manufacturer to see if a firmware update is available and how to install it. Firmware updates are usually free. |
|
TPM is disabled and requires attention. |
The trusted platform module is probably turned off in the system BIOS (Basic Input/Output System) or UEFI (Unified Extensible Firmware Interface). Refer to your device manufacturer's support documentation, or contact their technical support, for instructions on how to turn it on. |
|
TPM storage is not available. Please clear your TPM. |
The clear TPM button is on this page. You'll want to make sure you have a good backup of your data before proceeding. |
|
Device health attestation isn't available. Please clear your TPM. |
The clear TPM button is on this page. You'll want to make sure you have a good backup of your data before proceeding. |
|
Device health attestation isn't supported on this device. |
This means the device doesn't give us enough information to determine why TPM may not be working properly on your device. |
|
Your TPM isn't compatible with your firmware and may not be working properly. |
Check with your device's manufacturer to see if a firmware update is available and how to get and install it. Firmware updates are usually free. |
|
TPM measured boot log is missing. Try restarting your device. |
|
|
There is a problem with your TPM. Try restarting your device. |
If you still encounter problems after addressing an error message, contact your device manufacturer for assistance.
Select Clear TPM to reset your security processor to its default settings.
Caution: Make sure to back up your data before you clear the TPM.
Secure boot
Secure boot prevents a sophisticated and dangerous type of malware - a rootkit - from loading when your device starts. Rootkits use the same permissions as the operating system and start before it, which means they can completely hide themselves. Rootkits are often part of an entire suite of malware that can bypass local logins, record passwords and keystrokes, transfer private files, and capture cryptographic data.
You might have to disable secure boot to run some graphics cards, hardware, or operating systems such as Linux or earlier versions of Windows.
To learn more, see Secure boot.
Hardware security capability
The last section of the device security page displays information indicating the security capability of your device. Here's a list of messages and details:
|
Message |
Details |
|---|---|
|
Your device meets the requirements for standard hardware security. |
This means your device supports memory integrity and core isolation and also has:
|
|
Your device meets the requirements for enhanced hardware security. |
This means that in addition to meeting all the requirements of standard hardware security, your device also has memory integrity turned on. |
|
Your device has all Secured-core PC features enabled. |
This means that in addition to meeting all the requirements of enhanced hardware security, your device also has System Management Mode (SMM) protection turned on. |
|
Standard hardware security not supported. |
This means that your device does not meet at least one of the requirements of standard hardware security. |
Improving hardware security
If the security capability of your device isn't what you'd like it to be, you might need to turn on certain hardware features (such as secure boot, if supported) or change the settings in your system's BIOS. Contact your hardware manufacturer to see what features are supported by your hardware and how to activate them.
PC Manager
|
|
The PC Manager app may also be useful in this scenario. For more information, see Microsoft PC Manager. Note: Microsoft PC Manager isn't available in all locales. |