Secure Boot update from 2011 to 2023 certificates: Trusted Launch VMs (TVM) and Confidential VMs (CVM)
Original publish date: May 13, 2026
KB ID: 5085395
This article has guidance for:
-
Azure Trusted Launch Virtual Machines (TVM) and Confidential VMs (CVM) running Windows with Secure Boot enabled.
-
For the complete list of supported Windows operating systems, see the article: Trusted Launch for Azure virtual machines
In this article:
Introduction
Secure Boot is a UEFI firmware security feature that helps ensure that only trusted, digitally signed software runs during the device boot sequence. Microsoft Secure Boot certificates issued in 2011 begin expiring in June 2026.
To maintain Secure Boot protections and continued servicing of the early boot process, Azure Trusted Launch and Confidential virtual machines must be updated with both of the following:
-
Secure Boot 2023 certificates in virtual firmware
-
A Windows Boot Manager signed by the updated certificates
These components work together: the certificates establish trust in virtual firmware, and the Boot Manager must be updated to be signed by that trust.
To help prevent gaps in protection, verify that both components are updated and initiate updates where required.
If a VM continues to rely on the 2011 certificates after expiration, it can continue to boot and receive standard Windows updates. However, it will no longer receive new security protections for the early boot process, including updates to Windows Boot Manager, Secure Boot databases and revocation lists, or mitigations for newly discovered boot-level vulnerabilities.
To learn more, see When Secure Boot certificates expire on Windows devices.
Identify scenarios that require action
In most cases, Windows applies the Secure Boot 2023 certificates automatically through monthly updates on eligible devices, including supported Azure Trusted Launch and Confidential VMs with Secure Boot enabled. Some VMs might not qualify for automatic deployment if sufficient compatibility signals are not available. In these cases, administrative action might be required to initiate updates from within the guest operating system. For more information on how to get Secure Boot certificates updates, visit: Secure Boot Certificate updates: Guidance for IT professionals and organizations.
Secure Boot updates for Azure Trusted Launch and Confidential VMs involve two components:
-
Secure Boot certificates stored in virtual firmware (platform‑managed)
-
Windows Boot Manager (guest OS‑managed)
Virtual machines created after March 2024 typically already include the Secure Boot 2023 certificates in virtual firmware. These VMs generally require only a Windows Boot Manager update.
Long-running virtual machines created prior to March 2024 do not include the Secure Boot 2023 certificates in virtual firmware and require updates to both Secure Boot certificates and Windows Boot Manager.
Update operations are initiated from within the guest operating system through Windows servicing and rely on platform support to apply authenticated updates to Secure Boot variables in virtual firmware.
After identifying applicable scenarios, inventory your environment to determine which VMs require updates.
Actions required:
-
Ensure that guest VMs are updated with the March 2026 Windows update or later (April 2026 or later if using hotpatching). See more: Hotpatch for Windows Server.
-
Verify that all Azure Trusted Launch and Confidential VMs have the Secure Boot 2023 certificates and an updated Windows Boot Manager.
-
Initiate updates from within the guest operating system to apply Secure Boot certificate and Windows Boot Manager updates where required.
-
Audit the Windows System event logs: Event ID 1808 and Event ID 1801 or monitor the UEFICA2023Status registry key to confirm whether updated Secure Boot certificates have been applied and whether the Windows Boot Manager has been updated.
For devices that have not applied these updates, use the monitoring and deployment methods described in the Secure Boot playbook, Windows Server Secure Boot playbook for certificates expiring in 2026, and at https://aka.ms/GetSecureBoot for complete guidance.
Azure guest VM considerations
Review the following scenarios and required actions for session hosts:
|
VM Scenario |
Secure Boot Active? |
Action Required |
|
TVM or CVM with Secure Boot enabled |
Yes |
Update Secure Boot certificates and Windows Boot Manager |
|
TVM with Secure Boot disabled |
No |
No action needed |
|
Generation 1 VM |
Not supported |
No action needed |
Note: Standard security-type VMs do not have Secure Boot enabled.
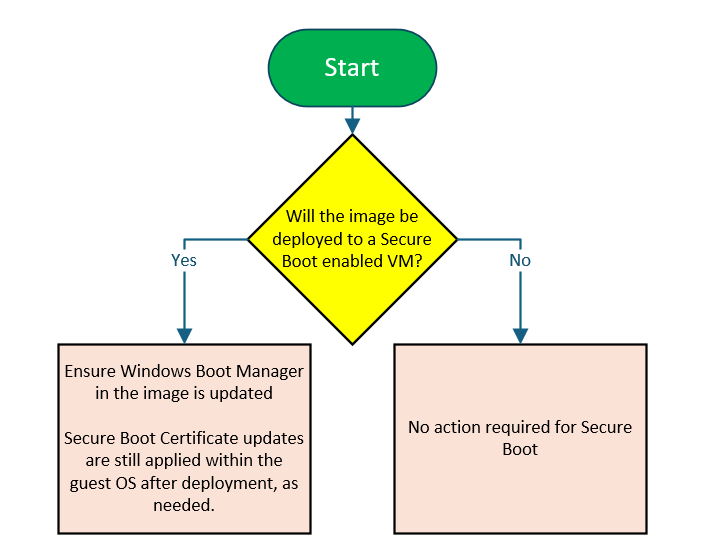
Golden image considerations
Review the following scenarios and required actions for images:
Note: Azure Marketplace images provide preconfigured starting points, vanilla or publishers’ default images, while Azure Compute Gallery images are used to store and distribute customized images. In both cases, images capture Windows Boot Manager but do not include Secure Boot firmware variables, which are applied at the virtual machine level.
Azure Compute Gallery and managed images capture operating system and boot loader state, including Windows Boot Manager, but do not include Secure Boot firmware variables. Secure Boot certificates, such as updates to the Secure Boot database (DB) or key exchange keys (KEK), are stored in the virtual firmware of the deployed virtual machine and are not captured during image generalization.
Applying Secure Boot updates within a golden image advances the Windows Boot Manager but does not persist Secure Boot certificates to virtual machines provisioned from that image. However, performing this update advances the Windows Boot Manager within the image.
Actions required:
-
Apply the Secure Boot 2023 update to the golden image before capturing it. Note: This advances the Windows Boot Manager but will not persist Secure Boot certificates to deployed virtual machines.
-
Restart the VM as required to allow the Boot Manager update to apply.
-
Verify that the update has completed before generalizing the image by running the following PowerShell command and confirming the value is set to Updated:
Get-ItemProperty "HKLM:\SYSTEM\CurrentControlSet\Control\SecureBoot\Servicing" | Select-Object UEFICA2023Status
Updating Windows Boot Manager within a golden image applies that update to virtual machines deployed or redeployed using the image. Newly provisioned Azure Trusted Launch and Confidential virtual machines include the Secure Boot 2023 certificates in virtual firmware and can safely use golden images with the updated Windows Boot Manager.
However, image‑based redeployments onto existing virtual machines created prior to March 2024 might apply the updated Windows Boot Manager to VMs whose firmware does not yet trust the corresponding Secure Boot 2023 certificates. In these cases, Secure Boot certificate updates should be applied within the guest operating system before advancing the Windows Boot Manager.
Other Azure resources considerations
|
Azure resource |
Created before April 2024? |
Action required |
|---|---|---|
|
Backup/snapshot of TVM or CVM |
Yes |
Boot the VM, apply updates, and then recapture |
|
Backup/snapshot of TVM or CVM |
No |
No action needed |
|
Azure Compute Gallery image captures with (image security type = TL or CVM) captures from TVM or CVM |
Yes |
Boot the VM, apply updates, and then recapture |
|
Azure Compute Gallery image captures with (image security type = TL or CVM) captures from TVM or CVM |
No |
No action needed |
Monitor update status
Monitoring and deployment for Secure Boot certificate updates in Azure Trusted Launch and Confidential virtual machines follows the same Windows servicing guidance used for physical and virtualized devices.
For detailed monitoring guidance, including how to inventory devices, verify firmware variable updates, and track update progress, see the Secure Boot Playbook for Windows Server and https://aka.ms/GetSecureBoot.
Deploy updates
Secure Boot certificate updates for Azure Trusted Launch and Confidential virtual machines are initiated from within the guest operating system using Windows servicing.
Follow the deployment guidance in the Secure Boot Playbook for Windows Server for:
-
automatic deployment via Windows Update
-
IT-initiated deployment methods
-
servicing registry keys
-
deployment sequencing
When using custom or reused virtual machine images, see Golden image considerations in this article before advancing the Windows Boot Manager.
Resources
-
Bookmark Get Secure Boot for more information about this change, detailed guidance for managing the Secure Boot certificate update, and answers to frequently asked questions.
-
Secure Boot Certificate updates: Guidance for IT professionals and organizations
-
For more details about Event Log events, see Secure Boot DB and DBX variable update events.
-
For more details about Secure Boot registry keys, see Registry key updates for Secure Boot: Windows devices with IT-managed updates.
If you have a support plan and need technical help, please submit a support request.
Change log
|
Change date |
Change description |
|
May 13, 2026 |
There are no changes in this article |