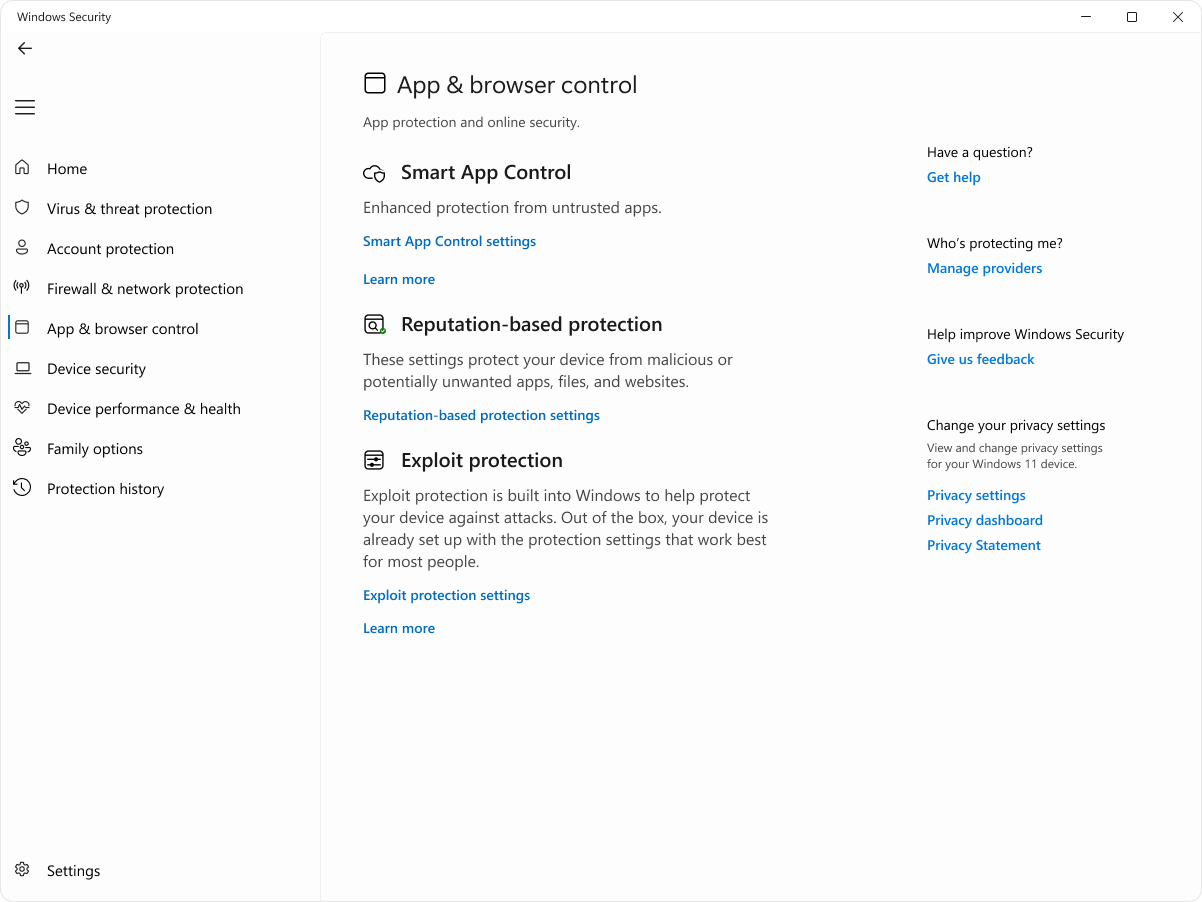
App & browser control in the Windows Security App
Applies To
The App & Browser Control page in the Windows Security app provides essential security settings that protect your Windows device from unsafe apps, files, websites, and downloads. By combining reputation‑based protection with exploit mitigation, it helps prevent malware, phishing attempts, and other security threats from compromising your system.
The page is divided into the following sections:
-
Smart App Control: Use this section to configure Smart App Control, which is a security feature designed to block apps that are potentially harmful, such as those that might slow down your PC, display unexpected ads, or offer unwanted software. Smart App Control leverages AI and cloud-based intelligence to predict the safety of an application, allowing only those deemed safe to run.
Note: Smart App Control is not available in Windows 10.
-
Reputation-based protection: This section allows you to configure Microsoft Defender SmartScreen, which is a security feature that protects from phishing attacks, malware, and potentially unwanted applications. It provides reputation-based protection by evaluating websites and downloads against a list of known malicious sites and files.
-
Exploit Protection: In this section you can configure several threat mitigations that can be applied to either the operating system or individual applications. These mitigations are designed to reduce the attack surface and make it more difficult for attackers to exploit vulnerabilities.
In the Windows Security app on your PC, select App & browser control, or use the following shortcut:
Smart App Control
Smart App Control adds significant protection from new and emerging threats by blocking apps that are malicious or untrusted. Smart App Control also helps to block potentially unwanted apps, which are apps that may cause your device to run slowly, display unexpected ads, offer extra software you didn't want, or do other things you don't expect.
Smart App Control works alongside your other security software, such as Microsoft Defender or non-Microsoft antivirus tools, for added protection.
Important:
-
Smart App Control can be used on new Windows 11 installs only. If you received it as part of a Windows update on an already running device, you won't be able to turn it on unless you reset your PC or re-install Windows.
-
For the best experience with Smart App Control be sure you have the latest Windows and Defender updates installed on your device.Check for updates
In the Windows Security app on your PC, select App & browser control > Smart App Control settings, or use the following shortcut:
The settings allow you to enable or disable Smart App Control, which can operate in three modes:
-
Evaluation mode: This is a period during which Windows tries to determine if you're a good candidate for Smart App Control. If you are a good candidate, it will automatically be turned on. If not, it will be turned off. Smart App Control won't block anything while it's in evaluation mode. Once the evaluation is complete, or if you manually switch Smart App Control on or off, you won't be able to return to evaluation mode unless you reinstall or reset Windows.
-
On: Smart App Control will notify you when apps are untrusted. Apps trusted by the prediction model and/or with valid signatures will run.
-
Off: Smart App Control won't notify you of untrusted apps. This can occur if it is manually turned off, or if during evaluation mode you were determined not to be a good candidate.
Do you have any questions about Smart App Control? Review Smart App Control Frequently Asked Questions.
Reputation-based protection
Reputation-based protection leverages what Microsoft knows about various sites, services, and publishers, as well as threats we've seen in action to help protect you from malicious or potentially unwanted apps, files, or websites.
In the Windows Security app on your PC, select App & browser control > Reputation-based protection or use the following shortcut:
Reputation-based protection settings
There are several kinds of reputation-based protection. Expand each section to learn more:
This toggle turns on Microsoft Defender SmartScreen to evaluate the reputation of apps and files you may download from the web.
When you're using the new Microsoft Edge as your browser, Microsoft Defender SmartScreen can help evaluate websites or downloads to see if they are known to be malicious, such as phishing sites, or tech support scams.
If you try to go to a site that is known to be dangerous, SmartScreen will show you a warning screen that clearly identifies the suspected threat and gives you a chance to close the browser tab before anything bad can happen.
When you attempt to download a file that SmartScreen finds suspicious, Edge warns you that the file may be untrusted and gives you the opportunity to cancel the download before it takes place.
Note: This feature is not available in Windows 10.
Phishing protection helps protect your password from being stolen, or phished, on malicious sites and apps pretending to be safe.
If you sign into Windows 11 using a password, phishing protection alerts you if you type that password into a malicious website or into an application connecting to a known malicious site. Phishing protection helps protect your password in four ways:
-
If you type your Microsoft account password into a site that SmartScreen finds malicious, phishing protection will alert you. It will also prompt you to change your password so attackers can't gain access to your account.
-
Reusing the same password makes it easy for attackers who compromise your password to gain access to your other accounts. Phishing protection can warn you if you reuse your Microsoft account password on other sites or apps and prompt you to change your password.
Tip: For an engaging short story about the dangers of password reuse see Cameron learns about reusing passwords.
-
Since it's unsafe to store your password in text editors, phishing protection can warn you if you type your password into Notepad or a Microsoft 365 Office application like Word or OneNote.
-
If you type your Microsoft account password into a website or app that SmartScreen finds suspicious, phishing protection can automatically collect information - such as content displayed, sounds played, and application memory - from that website or app to help identify security threats.
Under Phishing protection, select the settings you want. By default, you are only protected against entering your password into malicious content.
Important: Currently, only the typed password used to sign into Windows 11 can be protected.
Potentially unwanted apps (PUA) aren't malware, but they might display advertising, use your PC for crypto mining, or do other things you'd prefer they not do. Microsoft Defender tries to identify those apps for you and block them before they can install, or download, and cause issues with your system.
For more information see Protect your PC from potentially unwanted applications.
While Microsoft Defender SmartScreen can protect you from malicious files or apps you may encounter in the Microsoft Edge browser, SmartScreen for Microsoft Store provides another check on content that is used by Microsoft Store apps. This is just another layer of security to protect you.
Exploit protection
Exploit protection is already running and protecting your device, and your device is set up with the protection settings that work best for most people. However, you can always customize the settings for your device and the programs you run. If you manage devices and programs in an organization, you can use the export feature to share customized exploit protection settings across all of the devices in your organization.
In the Windows Security app on your PC, select App & browser control > Exploit protection or use the following shortcut:
Exploit protection settings
To learn more, see Customize exploit protection.